Wydawca: 8
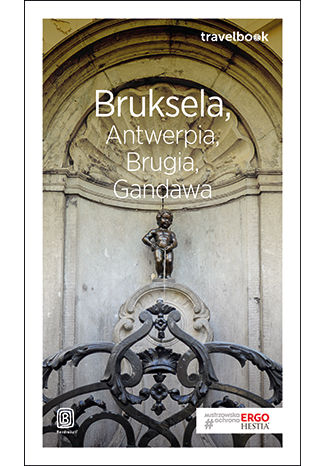
Bruksela, Antwerpia, Brugia, Gandawa. Travelbook. Wydanie 1
Beata Pomykalska, Paweł Pomykalski
Brunatna pajęczyna. Agenci Gestapo w okupowanym Krakowie i ich powojenne losy
Alicja Jarkowska
Bruno Kreisky. Polityka zagraniczna i dyplomacja wobec PRL (1959-1983)
Agnieszka Kisztelińska-Węgrzyńska