Видавець: 16
Karan Singh
Ceph is a unified, distributed storage system designed for excellent performance, reliability, and scalability. This cutting-edge technology has been transforming the storage industry, and is evolving rapidly as a leader in software-defined storage space, extending full support to cloud platforms such as Openstack and Cloudstack, including virtualization platforms. It is the most popular storage backend for Openstack, public, and private clouds, so is the first choice for a storage solution. Ceph is backed by RedHat and is developed by a thriving open source community of individual developers as well as several companies across the globe.This book takes you from a basic knowledge of Ceph to an expert understanding of the most advanced features, walking you through building up a production-grade Ceph storage cluster and helping you develop all the skills you need to plan, deploy, and effectively manage your Ceph cluster. Beginning with the basics, you’ll create a Ceph cluster, followed by block, object, and file storage provisioning. Next, you’ll get a step-by-step tutorial on integrating it with OpenStack and building a Dropbox-like object storage solution. We’ll also take a look at federated architecture and CephFS, and you’ll dive into Calamari and VSM for monitoring the Ceph environment. You’ll develop expert knowledge on troubleshooting and benchmarking your Ceph storage cluster. Finally, you’ll get to grips with the best practices to operate Ceph in a production environment.
Karan Singh, Michael Hackett, Vikhyat Umrao
Ceph is a unified distributed storage system designed for reliability and scalability. This technology has been transforming the software-defined storage industry and is evolving rapidly as a leader with its wide range of support for popular cloud platforms such as OpenStack, and CloudStack, and also for virtualized platforms. Ceph is backed by Red Hat and has been developed by community of developers which has gained immense traction in recent years. This book will guide you right from the basics of Ceph , such as creating blocks, object storage, and filesystem access, to advanced concepts such as cloud integration solutions. The book will also cover practical and easy to implement recipes on CephFS, RGW, and RBD with respect to the major stable release of Ceph Jewel. Towards the end of the book, recipes based on troubleshooting and best practices will help you get to grips with managing Ceph storage in a production environment. By the end of this book, you will have practical, hands-on experience of using Ceph efficiently for your storage requirements.
Michael Hackett, Vikhyat Umrao, Karan Singh, Nick...
This Learning Path takes you through the basics of Ceph all the way to gaining in-depth understanding of its advanced features. You’ll gather skills to plan, deploy, and manage your Ceph cluster. After an introduction to the Ceph architecture and its core projects, you’ll be able to set up a Ceph cluster and learn how to monitor its health, improve its performance, and troubleshoot any issues. By following the step-by-step approach of this Learning Path, you’ll learn how Ceph integrates with OpenStack, Glance, Manila, Swift, and Cinder. With knowledge of federated architecture and CephFS, you’ll use Calamari and VSM to monitor the Ceph environment. In the upcoming chapters, you’ll study the key areas of Ceph, including BlueStore, erasure coding, and cache tiering. More specifically, you’ll discover what they can do for your storage system. In the concluding chapters, you will develop applications that use Librados and distributed computations with shared object classes, and see how Ceph and its supporting infrastructure can be optimized. By the end of this Learning Path, you'll have the practical knowledge of operating Ceph in a production environment.This Learning Path includes content from the following Packt products:• Ceph Cookbook by Michael Hackett, Vikhyat Umrao and Karan Singh• Mastering Ceph by Nick Fisk• Learning Ceph, Second Edition by Anthony D'Atri, Vaibhav Bhembre and Karan Singh
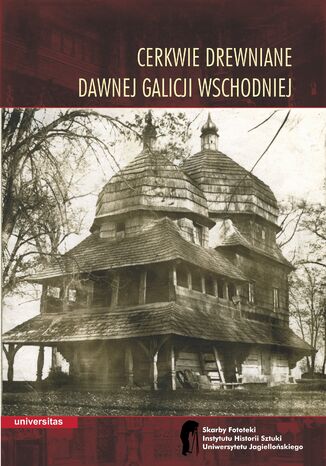
Cerkwie drewniane dawnej Galicji Wschodniej
Wojciech Walanus
Książka Cerkwie drewniane dawnej Galicji Wschodniej jest pierwszym tomem serii, w której publikowane będą wybrane, najcenniejsze fotografie ze zbiorów Fototeki Instytutu Historii Sztuki Uniwersytetu Jagiellońskiego, jednego z najstarszych archiwów fotograficznych o profilu historyczno-artystycznym na ziemiach polskich (rok założenia 1884). Tom zawiera dwa naukowe eseje, autorstwa Piotra Krasnego i Wojciecha Walanusa: pierwszy jest wprowadzeniem w problematykę historyczno-artystyczną i konserwatorską drewnianych świątyń obrządku wschodniego na ziemiach Rzeczypospolitej, drugi przedstawia pokrótce dzieje zbiorów Fototeki, okoliczności powstania zaprezentowanych w tomie fotografii oraz sylwetki ich autorów. Zasadniczą częścią książki jest album ze stu szesnastoma reprodukcjami archiwalnych odbitek, na których utrwalono wygląd ponad siedemdziesięciu cerkwi, przeważnie już nie istniejących lub przekształconych. Albumowi towarzyszy katalog, w którym zostały podane najważniejsze fakty historyczne dotyczące poszczególnych budowli (wraz z podstawową bibliografią) oraz szczegółowe informacje o fotografiach (technika, wymiary, datowanie, autorstwo, inskrypcje, znaki własnościowe itd.).
Krystyna Warchał
Przedmiotem pracy są językowe wykładniki stopnia pewności sądów w artykułach naukowych z dziedziny językoznawstwa w języku angielskim i polskim. Punktem wyjścia podjętych badań jest przekonanie, że różne tradycje intelektualne, w jakich kształtowała się polska i angielska komunikacja akademicka — tradycje odmiennie postrzegające status wiedzy naukowej i proces jej tworzenia, relację między autorem i czytelnikiem, czy wreszcie sam akt pisania i stopień dialogowości tekstu naukowego — mogą znajdować odzwierciedlenie w różnych przeświadczeniach dotyczących tego, czym jest fakt naukowy, a co pozostaje w sferze hipotez, założeń i propozycji oczekujących na potwierdzenie i akceptację środowiska akademickiego. Różnice te z kolei sugerowałyby, iż autorzy wywodzący się z tych dwóch kręgów kulturowych mogą przywiązywać różną wagę do wyraźnego oznaczania treści hipotetycznych oraz sądów, którym towarzyszy wysoki stopień pewności, oznaczać je w różny sposób, z różną częstotliwością i w różnych miejscach wywodu. Niniejsza praca podejmuje próbę ustalenia, czy różnice takie istnieją i, jeśli tak, których wykładników modalności epistemicznej dotyczą i jak przebiegają. Praca może stanowić głos w dyskusji nad różnicami w stylach argumentacji akademickiej charakterystycznych dla poszczególnych kultur i dyscyplin, wnieść dane do badań porównawczych nad znaczeniami epistemicznymi i ich funkcją w różnych typach dyskursu oraz być punktem odniesienia dla dalszych analiz uwzględniających inne języki, gatunki i dyscypliny.
Dale Meredith, Christopher Rees
With cyber threats continually evolving, understanding the trends and using the tools deployed by attackers to determine vulnerabilities in your system can help secure your applications, networks, and devices. To outmatch attacks, developing an attacker's mindset is a necessary skill, which you can hone with the help of this cybersecurity book.This study guide takes a step-by-step approach to helping you cover all the exam objectives using plenty of examples and hands-on activities. You'll start by gaining insights into the different elements of InfoSec and a thorough understanding of ethical hacking terms and concepts. You'll then learn about various vectors, including network-based vectors, software-based vectors, mobile devices, wireless networks, and IoT devices. The book also explores attacks on emerging technologies such as the cloud, IoT, web apps, and servers and examines prominent tools and techniques used by hackers. Finally, you'll be ready to take mock tests, which will help you test your understanding of all the topics covered in the book.By the end of this book, you'll have obtained the information necessary to take the 312-50 exam and become a CEH v12 certified ethical hacker.
Hemang Doshi
With cyber threats on the rise, IT professionals are now choosing cybersecurity as the next step to boost their career, and holding the relevant certification can prove to be a game-changer in this competitive market. CISM is one of the top-paying and most sought-after certifications by employers.This CISM Certification Guide comprises comprehensive self-study exam content for those who want to achieve CISM certification on the first attempt. This book is a great resource for information security leaders with a pragmatic approach to challenges related to real-world case scenarios. You'll learn about the practical aspects of information security governance and information security risk management. As you advance through the chapters, you'll get to grips with information security program development and management. The book will also help you to gain a clear understanding of the procedural aspects of information security incident management.By the end of this CISM exam book, you'll have covered everything needed to pass the CISM certification exam and have a handy, on-the-job desktop reference guide.
Hemang Doshi
CISM is a globally recognized and much sought-after certification in the field of IT security. This second edition of the Certified Information Security Manager Exam Prep Guide is up to date with complete coverage of the exam content through comprehensive and exam-oriented explanations of core concepts. Written in a clear, succinct manner, this book covers all four domains of the CISM Review Manual.With this book, you’ll unlock access to a powerful exam-prep platform which includes interactive practice questions, exam tips, and flashcards. The platform perfectly complements the book and even lets you bring your questions directly to the author.This mixed learning approach of exploring key concepts through the book and applying them to answer practice questions online is designed to help build your confidence in acing the CISM certification.By the end of this book, you'll have everything you need to succeed in your information security career and pass the CISM certification exam with this handy, on-the-job desktop reference guide.